Environment/Versions:
WebLogic Server Version: 12.2.1.4.0 (onpremise)
Oracle IDCS (oracle cloud)
Atn/Atz: SAML
Usecase:
Authenticate and Authorize ADF application deployed to weblogic with SSO.
Weblogic is configured as a service provider (SP) and IDCS is configured as the Identity provider (IDP).
There's a loadbalancer present in the architecture which manages traffic to all managed servers in the cluster.
Currently, when a user attempts to access the protected resource, browser gets redirected to the IDCS credentials challenge page for username and password.
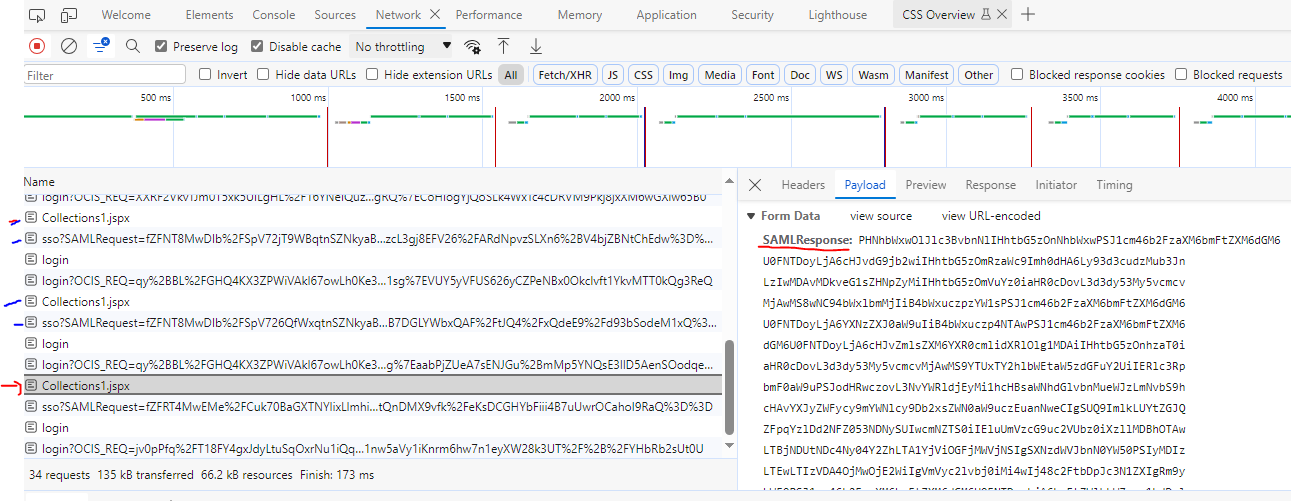
When this is entered correctly, then we hit an infinite 302 status as seen in the image below
Note:
On IDCS, the Assertion Consumer URL is currently https://{LB_URL}/{APP_CONTEXT}/Collections1.jspx - "Perhaps this is responsible for the 302's),
When we changed the Assertion Consumer URL to https://{LB_URL}/saml2/sp/acs/pc - we hit a 404 http response.
WLS Configurations done - [in/correctly]
- SAML2IdentityAsserter has been configured in the security realm,
- managed servers federation services > saml2.0 general and service provider configuration.
Questions:
- My assumption is that the SAMLResponse should be handled by WLS and assertion done automatically using the shipped identity asserter- is this correct?
- Why is the /saml2/sp/acs/pc endpoint giving a 404 response?
- Do I have to develop a custom servlet in my ADF application to handle the SAMLResponse myself?